Ways for hacking any account (Facebook,Gmail,Yahoo,Twitter etc)
Phishing
Phishing is the creation of email messages and web Pages in such a way that the replicas of existing web sites to fool users and instruct them to submit their personal or financial details into fraudsters fake pages.Steps involved in phishing
►Making necessary files -copy of the web page of the service provider(facebook, gmail, twitter etc)with some changes so that instead of password & id going to the their database it goes to a user specified file, log.txt(in which the username & password will be stored)
►Upload all of the files to any free webhosting sites like:
www.yourfreehosting.net
www.esmartstart.com
www.110mb.com
www.t35.com etc
www.yourfreehosting.net
www.esmartstart.com
www.110mb.com
www.t35.com etc
►Sending link of the fake page to the victim.
Once the victim fills his details on the fake page, all his typed id and password is stored in “log.txt” as you will make some changes in the html of the web page. Just open log.txt to get hacked id and password.
Search YouTube For Softwares
When you search you tube(or similar networks) with the query ‘hack facebook id’ (or any other) you will get lots of videos showing a simple software which gives you the password just by typing the victim’s ‘E-mail ID’ and pressing on ‘Hack’ button.Well 99% of them are fake,even I tried some of the famous ones like Webmail Hack etc.They will redirect you to a page through a link where they get paid for every download.They just want to earn money and will waste time.But it’s 99% may be you get the one you were looking for.To check the truthfulness of the video you can refer to the video’s comments,they could really help to know if the video is fake or not.
Social Engineering
The simplest way to describe Social Engineering would be that it is a means of gathering information about a target using social means rather than purely electronic means.A “Social engineer”tries to get the target to divulge as much information about them as possible in order to improve their chances at guessing the victim’s password.He may crack your password by using the information collected like ☻Your partner, child, or pet’s name, possibly followed by a 0 or 1 (because they’re always making you use a number, aren’t they?)☻The last 4 digits of your social security number.☻Your city, or college, football team name.☻Date of birth – yours, your partner’s or your child’s.
Statistically this should probably cover about 20% of you.
Key Logging
Keystroke logging (often called keylogging) is the action of tracking (or logging) the keys struck on a keyboard locally or remotely,in a manner so that the person using the keyboard is unaware that his actions are being monitored.
Steps involved in hacking-
►Download a keylogger eg- L33t’s Keylogger, Beyond KeyLogger etc.
►Set the details like email id,name of the service provider(gmail,ymail),time interval(at what intervals you want the keystrokes)
►Bind the keylogger with a genuine file, it may be a software or image so that the victim is not able to suspect you.
►Spread the file.You can spread it through forums, or pendrives,or mails.
Brute Force & Dictionary Attacks
Well, theoretically,any password can be cracked using a cracking software(eg- Advanced Archive Hacker which is used to crack winrar password) given enough time, but when you put in reasonable constraints, you will find that beyond a point, nothing can be done.
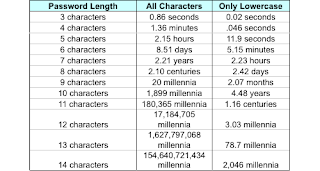
When we talk about complexity, calculating it depends on what all characters are permissible in a password. A single character of a password may contain 26 letters, their capital counterpart, 10 digits, and 32 special characters, plus the white space character making to a total of 95 possibilities. So a 4 character password we have 95*95*95*95(81450625) possibilities. You can’t even imagine how much time and space would be required to hack a 10 character password. Also, adding just one capital letter and one asterisk would change the processing time for a 8 character password from 2.4 days to 2.1 centuries.
Please comment if you any query with this post.
Here are the security tips for protecting your account & password and how-to not become a victim of these attacks.
Disclaimer:-This post is totally intended for educational purpose and does not in anyway encourage hacking.I will not be responsible for what you do with this information.The words “Hack” and “Hacking” should be taken or considered as “Ethical Hack” or “Ethical Hacking”.